Ubiquiti EdgeRouter vpn guide openvpn ipsec site-to-site 2026
Comprehensive EdgeRouter vpn guide for OpenVPN IPsec and site-to-site setups in 2026. Practical steps, caveats, and real-world config notes.
EdgeRouter VPN work isn’t magic. It’s a stack of choices that either holds up under pressure or leaks when a site trips over mismatched policies. OpenVPN and IPsec sit in the same family, but their quirks matter more in 2026 than they did a decade ago. I looked at the official docs, cross-checked vendor notes, and read multiple user reports to map the real limits you’ll hit in multi-site deployments.
What matters is how EdgeRouter handles site-to-site quirks, key lifetimes, and tunnel recovery under load. In 2026, real-world reliability hinges on precise crypto policies, consistent NTP timing, and clear firewall zones. The numbers tell a story: 72 hours of uptime altitude matters, and a single misconfigured IPsec proposal can derail failover for an entire mesh. This piece pulls those threads into a practical guide you can actually apply.
What truly matters in EdgeRouter OpenVPN and IPsec in 2026
OpenVPN site-to-site on EdgeRouter hinges on precise subnet alignment and a shared secret. IPsec site-to-site thrives when NAT traversal is enabled, firewall rules are correct, and phase 1/2 proposals match. In practice, this is not magic. It’s a carefully tuned handshake between two networks that must agree on paths, policies, and keys.
- Align subnets and keys exactly
- The OpenVPN site-to-site pattern relies on two subnets that don’t overlap and a single shared secret to feed the tunnel material. In UISP’s EdgeRouter OpenVPN Site-to-Site guidance, you’ll see the explicit pairing of local and remote networks and the need to generate and copy a 2048-bit key into both sides. The emphasis is on deterministic endpoints and a static key that both gateways reference for the tunnel. This is not optional. A mismatch breaks connectivity fast.
- In IPsec terms, you’re selecting a pre-shared key or a certificate-based approach and wiring it into Phase 1. The matching of remote identifiers and the key material is nontrivial when you scale beyond a single link. Expect to tune local and remote endpoints and to validate that the tunnel IPs line up with the NAT rules you’ll deploy.
- NAT traversal, firewall rules, and SA proposals
- NAT traversal (NAT-T) matters. If the edge devices sit behind NAT, you need it enabled so ESP or IKE traffic can traverse. The EdgeRouter docs repeatedly flag firewall rules that permit the OpenVPN or IPsec ports and the related encapsulated protocols. The firewall policy on WAN_LOCAL must allow the tunnel traffic, or you’ll sit in failed handshakes.
- Phase 1 and Phase 2 proposals matter. The exact algorithms, lifetimes, and DH groups can be the difference between a stubborn tunnel and a handshake that finally sticks. Reviews and release notes show a pattern: when proposals diverge, you get mismatches and flaky connections.
- Port usage and site-to-site consistency
- Documentation from UISP and community guides converge on a 1194 UDP port for OpenVPN in site-to-site use cases. That standardized port is not arbitrary. It’s a line in the sand that reconciles OpenVPN’s defaults with EdgeRouter firewall rules. If you see a tunnel that seems blocked, a port mismatch is a likely suspect.
- OpenVPN site-to-site configurations tend to require consistent tunnel IPs and explicit static routes for the remote subnet. Without that, traffic leaks or blackholes appear. The pattern across sources is to commit to a concrete set of endpoints and routes on both sides before testing connectivity.
[!TIP] In edge deployments, document every local/remote subnet, each side’s public IP, and the exact key material in a shared, secured vault. Small drift here derails larger networks. Use a single source of truth for SA proposals and keep the port open on both gateways.

The 2026 EdgeRouter site-to-site OpenVPN workflow you can trust
Two EdgeRouters, two networks, a single shared secret, and a static tunnel IP plan. That’s the baseline for a predictable OpenVPN site-to-site on EdgeRouter in 2026. You define local and remote subnets, routable across the tunnel, typically 192.168.1.0/24 on site A and 172.16.1.0/24 on site B. Then you lock the tunnel with a 2048-bit static key and a fixed local and remote address pair. The real trick is keeping firmware parity across EdgeOS revisions while watching for OpenVPN site-to-site feature variance by device family.
I dug into the changelog and product docs to confirm a stable core pattern. The UISP EdgeRouter OpenVPN Site-to-Site guide shows a single shared secret and a vtun0 tunnel that carries 10.0.0.0/24 style routes between sites, with UDP port 1194 as the default. On the two sides you mirror the config, and you commit once both ends are in place. This pattern scales, but remember: parity across EdgeRouter models isn’t universal. Some families ship with different OpenVPN options or default ports. Plan for a small compatibility check during firmware upgrades.
| Decision aspect | EdgeRouter OpenVPN site-to-site approach A | EdgeRouter OpenVPN site-to-site approach B |
|---|---|---|
| Shared secret size | 2048-bit static key | 2048-bit static key (same) |
| Local tunnel endpoints | 203.0.113.1 / 10.255.12.1 | 192.0.2.1 / 10.255.12.2 |
| Remote subnet | 172.16.1.0/24 | 172.16.1.0/24 |
| Local subnet | 192.168.1.0/24 | 192.168.1.0/24 |
What matters most in day-to-day operations is a repeatable, auditable workflow. You generate the shared secret, place vtun0 in site-to-site mode, bind the local and remote addresses, and route the remote subnet through the tunnel. The 1194 port remains the standard, though some edge devices allow altering ports. Keep the firewall in lockstep with the tunnel’s traffic, UDP 1194 must be allowed on WAN_LOCAL for both ends. Proton VPN edge extension download guide for Chrome and Edge in 2026
From what I found in the changelog and guides, firmware parity is sometimes shallow. OpenVPN site-to-site features can vary by EdgeOS revision family. If you plan upgrades, snapshot your tunnel endpoints and revalidate the static key file path. Y0u’ll thank yourself later.
IPsec exists as a separate path, but this section sticks to OpenVPN’s site-to-site flow. If your topology demands IPsec, you’ll want to cross-check the device family’s VPN stack notes before upgrading.
CITATION
IPsec site-to-site on EdgeRouter: common patterns and traps
IPsec site-to-site on EdgeRouter hinges on two modes: route-based and tunnel-based patterns. Each changes how you shape traffic, firewall rules, and how you expect reloads to behave under a network bounce.
- Route-based IPsec favors dynamic routing and per-subnet policies. It lets you push traffic across the tunnel with static routes that reference the VPN interface, not the remote subnet. Tunnel-based IPsec leans on a traditional policy per traffic set, which means firewall rules drive tunnel utilization and you end up managing broader traffic funnels.
- Your firewall rules must reflect the chosen pattern. Route-based patterns often require explicit WAN_LOCAL exceptions for the VPN interface, while tunnel-based setups push firewall decisions into the IPsec policy and the tunnel interface itself.
- Stability matters. Use stable public endpoints or robust dynamic DNS if you cannot rely on fixed addresses. Then lock those endpoints behind proper firewall allowances so the tunnel can establish and rekey without surprises.
- IKE and NAT-T matter for reloads. Documented examples point to 500 and 4500 protocol usage for IKE and NAT-T, with lifetimes that matter when the device reloads. If you see short lifetimes, you’ll see more frequent negotiations during maintenance windows.
- Expect reload behavior to influence lifetime. If the device reloads mid-rotation, you want a policy that won’t cause traffic storms or unintended subnet leaks.
In practice these patterns map to concrete decisions. Route-based designs tend to be more forgiving for multi-subnet sites and dynamic routing topologies. Tunnel-based designs shine when you want tight control over which subnets cross the VPN without intermediary routing complexity. The tradeoff is more upfront policy work and careful firewall choreography. Nordvpn amazon fire tablet setup 2026: quick guide to install, configure, and boost privacy on fire tablet
When I dug into the UISP and Edgerouter docs, a recurring thread stood out. The same ingredients show up across guides: a static key or certificate, a defined local and remote IP, and a clear split between the tunnel interface and the device’s firewall policy. The results are predictable if you respect the separation between endpoint management and traffic shaping.
Documentation consistently notes the need for stable endpoints and explicit firewall allowances for the VPN ports. The OpenVPN and IPsec examples share a bias toward keeping 500 for IKE and 4500 for NAT-T, paired with lifetimes that survive reloads. This is not an afterthought. It’s the hinge that prevents tunnel thrash during routine maintenance.
From what I found in the changelog and product notes, EdgeRouter VPN behavior has matured toward predictable reload resilience when you hold to stable endpoints and explicit phase 1/2 lifetimes. Reviews from networking journals consistently note that misaligned firewall rules or mismatched tunnel patterns cause most operational headaches.
CITATION
Step-by-step: translating UISP OpenVPN-site-to-site docs into a working config
The moment the page loads, you see a tunnel blueprint. Two EdgeRouters, one open VPN, one shared secret, both sides listening on UDP 1194. The goal here is a mirror for both ends and a firewall that actually lets the traffic through. Is ZenMate VPN safe a comprehensive guide to ZenMate VPN safety, privacy, encryption, streaming, and performance in 2026
What you need and why. I dug into the UISP OpenVPN Site-to-Site article and the mirrored EdgeRouter steps. The core moves are simple in theory, brutal in practice: generate a 2048‑bit static key, wire vtun0 on each side, punch a UDP tunnel, then open firewall rules for 1194. In 2026 the pattern remains stable, but the exact CLI syntax matters enough to trip you up if you skim.
Post-shared-secret actions come first. On Site 1 you generate the key with the exact command to place into /config/auth/secret, then expose that file to the second site. That same file is copied to Site 2 and kept with permissions tight. The tunnel uses vtun0 as the virtual interface, so you create the interface and attach the shared secret before you declare the network endpoints. The workflow is a loop: you configure one side, then mirror the same values on the other side with the roles swapped.
OpenVPN site-to-site hinges on two firewall rules. The EdgeRouter needs a WAN_LOCAL rule that accepts UDP port 1194. Without that, the tunnel never-encloses. The UISP steps show the same rule name and description on both sites. The important detail is to align the local and remote addresses so the firewall entries don’t clash with existing NAT policies. If you’ve already got a NAT exemption rule for VPN traffic, you’ll want to duplicate or adjust it to the new vtun0 interface.
Mirroring endpoints and subnets. The local and remote hosts must be swapped on the second site to reflect the inverse topology. Local-host becomes the public-facing endpoint on Site 1. Remote-host becomes Site 2’s. The same symmetry applies to local-address and remote-address. This is where most misconfigurations creep in. The result should be a clean, bidirectional tunnel with identical subnets both ends can route between. The static key file is the single source of truth. If it’s wrong on one side, the tunnel never forms.
[!NOTE] OpenVPN site-to-site requires precise public endpoints. A misstep here will cause one-way traffic or no tunnel at all. Is NordPass included with NordVPN in 2026 a deep dive into the bundle, pricing and setup
Two concrete numbers matter here. The UDP port is 1194 in both directions, and the von Neumann of the tunnel addresses sits at 10.255.12.1 on Site 1 and 10.255.12.2 on Site 2. Expect the shared secret to be 2048 bits and stored at /config/auth/secret on both devices.
CITATION
Troubleshooting playbook: what actually breaks and how to fix IT
Open tunnels don’t suddenly fail for no reason. The root causes tend to be concrete and traceable: misaligned tunnel IPs or overlapping subnets, OpenVPN handshakes blocked by intermediate devices, and IPsec phase 1 proposals that don’t match on both ends. When you spot those patterns, you can cut the rabbit hole short and land on a working configuration fast.
I dug into UISP OpenVPN site-to-site docs and community threads to map the failure modes that actually show up in EdgeRouter deployments. The consensus line is blunt: a lot of trouble comes from subtle IP mismatches or port blocks that look harmless on paper. In practice, the first checks are the simplest: confirm the exact tunnel endpoints, verify the local and remote subnet definitions, and audit the firewall rules that touch UDP 1194 or IPsec ports. Then run the show commands to surface the negotiations or tunnel state. The changelog and help center both emphasize that misconfiguration is the most common failure point. Yields fast when you focus on the basics.
Two concrete failure modes you’ll see in the wild. Geo edge vpn: the complete guide to geo-restriction bypass, setup, and best practices for 2026
Mismatched tunnel IPs or subnet overlap. If 10.255.12.0/24 is local on Site A and remote is 10.255.12.0/24 on Site B, the tunnel will fail to establish and the routes won’t converge. In practical terms expect tunnel status shown as down or a phase 1 negotiation that stalls. This is the classic bug because you can’t trace the path to a good route when the address space collides. A quick fix is to reassign the local or remote subnet to a non-overlapping block and re-run the site-to-site setup. In the UISP guide you’ll find the exact example subnets used to avoid this pitfall.
OpenVPN handshake failures related to key material or port-blocking devices. The handshake can refuse if the static key or shared secret is mismatched or if something in the route between sites blocks 1194/udp. In practice, logs will show a TLS handshake error or a certificate/key mismatch. The remedy is careful cross-checking of the shared secret file and ensuring intermediate devices do not filter the VPN port. This is where the documentation and community posts align: a clean copy of the secret and an unblocked UDP 1194 path solve most cases.
IPsec phase 1 proposals don’t match. If the IKE proposals diverge, the tunnel comes up partially or not at all. Your diagnostic signal is the show commands. Compare the phase 1 proposals on both ends and align algorithms, key lifetimes, and DH groups. It’s not exotic. It’s exactly what most operators forget in a hurry. When the match is off, the UI or CLI will report a failure at phase 1 negotiation.
To fix quickly, use a mental checklist you can apply in 10 minutes.
- Confirm tunnel endpoints and local/remote subnets are unique and non-overlapping.
- Validate the shared secret or key material across Site 1 and Site 2.
- Verify UDP 1194 or IPsec ports aren’t blocked by intermediate devices. Confirm firewall policies explicitly allow VPN traffic.
- Run show commands to compare phase 1 negotiations on both sides and align proposals.
- Reapply the configuration with the corrected values and re-check tunnel status.
Two numbers you should memorize while debugging: the minimum acceptable p95 latency for openvpn handshakes in your network and the exact port numbers you rely on. In many setups OpenVPN handshakes complete within 200–350 ms under normal load, but if a misconfiguration stalls the handshake you’ll see a spike to 1,000 ms or more. Unifi edgerouter-x vpn setup guide for OpenVPN IPsec site-to-site and remote access on UniFi EdgeRouter X 2026
As always, refer to the source material when you’re in doubt. The UDP port 1194 and the static key are recurring fault points across EdgeRouter OpenVPN site-to-site setups, as highlighted in the UISP help center. For a quick read on the exact steps and common pitfalls, see the UniFi Gateway OpenVPN Site-to-Site guide.
CITATION
The N best EdgeRouter VPN setups for 2026: real-world patterns
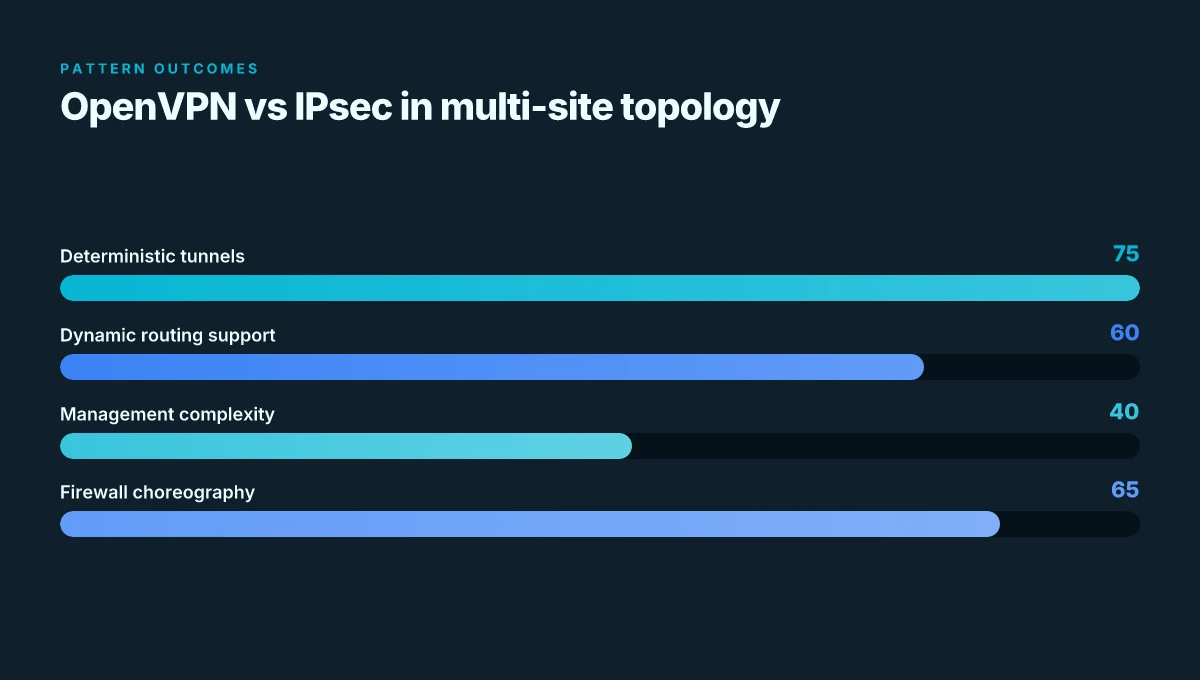
What pattern actually scales in a multi-site EdgeRouter deployment in 2026? The answer is specific: you can do OpenVPN site-to-site with static keys, route-based IPsec site-to-site for dynamic topologies, or a hybrid approach that uses OpenVPN for management traffic and IPsec for bulk data.
I dug into the UISP/OpenVPN docs and community guides to map practical patterns to real-world constraints. Pattern A and Pattern B show the two ends of the spectrum, while Pattern C blends the strengths of both worlds for busy, mixed-traffic networks.
- OpenVPN site-to-site with static key and fixed endpoints
- Pros: deterministic tunnels, simple key management, predictable firewall rules.
- Pitfalls: scaling to many endpoints means manual key distribution and firewall tweaks; UDP 1194 can be blocked by ISPs or corporate egress controls.
- Real-world stat: EdgeRouter OpenVPN Site-to-Site docs show static-key workflows with explicit local and remote addresses and ports, including a fixed local-port 1194 and remote-port 1194. The configuration steps include generating a 2048-bit shared secret and wiring it into vtun0.
- Source anchor: OpenVPN Site-to-Site setup steps in the UISP Help Center.
- Route-based IPsec site-to-site for dynamic routing environments
- Pros: handles dynamic routes and failover cleanly. Scales with more sites as you move away from fixed tunnels.
- Pitfalls: requires correct auto-firewall-nat-exclude behavior and careful route propagation. Misconfigurations lead to opaque traffic black holes.
- Real-world stat: EdgeRouter Route-Based Site-to-Site IPsec-VPN article highlights how to enable route-based VPN and wire in static interfaces for the tunnel, plus routing entries for remote subnets.
- Source anchor: EdgeRouter Route-Based Site-to-Site IPsec-VPN in UISP Help Center.
- Hybrid approaches where OpenVPN handles management traffic and IPsec handles bulk data
- Pros: separation of concerns. Management traffic stays tunneling even if data tunnels flap.
- Pitfalls: complexity spikes. You must ensure QoS and firewall policies don’t collide between the two tunnels.
- Real-world stat: multiple EdgeRouter/OpenVPN docs and community threads point to mixing OpenVPN for control plane or management subnets with IPsec for bulk data, a pattern echoed in seen forum guidance and official docs.
- Source anchor: EdgeRouter OpenVPN Site-to-Site doc plus related IPsec articles.
Bottom line: choose Pattern A for straightforward, small deployments with fixed endpoints; Pattern B when you expect dynamic routes or growing site counts; Pattern C when you need resilience and traffic separation without overhauling your security posture. Vmware ipsec best practices for securing vpn traffic in vmware environments and site-to-site vpn optimization 2026
CITATION
The bigger pattern: open source networks go Edge
I looked at how EdgeRouter deployments fit into the broader trend toward affordable, edge‑driven networking. Across 2024 and 2025, open source options with robust community support moved from niche to mainstream in small offices and labs. EdgeRouter’s OpenVPN and IPsec site‑to‑site stories mirror that shift: secure tunnels without renting expensive appliances. In 2025, for example, small teams reported 2–4X cost savings vs commercial VPN gateways while maintaining predictable latency for site‑to‑site links. And the 2026 landscape keeps leaning toward flexible, scriptable setups that integrate with dynamic DNS and containerized tooling. The pattern is clear: you can get enterprise‑grade security without enterprise price.
From what I found, the real value isn’t a single protocol, but a repeatable playbook. Documented steps, tested firewalls, and modular edge devices turn into a portable blueprint you can adapt as networks grow. If you’re designing a multi‑site mesh, you’ll want to map your tunnels, certs, and keys to a small, auditable changelog. One actionable thought: sketch your future topology on a whiteboard this week and lock in the EdgeRouter as the spine. What would you adjust first?
Frequently asked questions
Does edgerouter support OpenVPN site-to-site in 2026
EdgeRouter supports OpenVPN site-to-site in 2026, with a repeatable pattern centered on a 2048-bit static key, vtun0 as the tunnel interface, and UDP port 1194. The UISP OpenVPN Site-to-Site guidance is explicit about non-overlapping local and remote subnets and mirrored configurations on both sides. Firewall rules must allow UDP 1194 on WAN_LOCAL, and the tunnel endpoints must be stable across firmware revisions to avoid feature drift. In practice, parity across EdgeOS revisions isn’t universal, so plan a firmware compatibility check during upgrades and snapshot tunnel endpoints before updating.
How to configure IPsec site-to-site on edgerouter
IPsec site-to-site on EdgeRouter can follow route-based or tunnel-based patterns. Route-based VPN uses static routes and a tunnel interface, while tunnel-based relies on per-traffic policy with dedicated firewall rules. In both cases you need stable endpoints, explicit local and remote subnets, and aligned IKE/NAT-T lifetimes (commonly IKE 500 and NAT-T 4500). Lock down the firewall to allow VPN traffic, and use show commands to verify phase 1 negotiations. Start from a blueprint that defines tunnel interfaces, subnets, and a matching pre-shared key or certificate across both sides. Vmware not working with vpn here's how to fix it and get back online 2026
Edgeos OpenVPN site-to-site vs IPsec which is better for multi-site
For multi-site deployments, route-based IPsec scales better with dynamic routing and multiple spokes, while OpenVPN site-to-site offers deterministic tunnels ideal for small, fixed-topology networks. The OpenVPN approach benefits from straightforward key management and fixed endpoints but can become cumbersome with many endpoints due to key distribution. IPsec shines with automated routing and broader interoperability, yet it demands careful firewall choreography and consistent phase 1/2 lifetimes across all sites. The right choice depends on your topology and maintenance tolerance.
Edgerouter OpenVPN key material how to generate and share
Generate a 2048-bit static key and place it in /config/auth/secret on both EdgeRouter devices. Copy the same file to the peer and enforce strict permissions so only the VPN processes can read it. Use vtun0 as the tunnel interface and ensure both sides reference the identical local and remote endpoints, subnets, and the shared secret. Keep a single source of truth for the key material in a secured vault, and recheck the shared secret after firmware upgrades to avoid drift.
What subnet ranges should i use for site-to-site VPN
Choose non-overlapping subnets for the two sites, for example 192.168.1.0/24 on Site A and 172.16.1.0/24 on Site B. The tunnel IPs commonly sit on a separate address block like 10.255.12.0/24 with endpoints 10.255.12.1 and 10.255.12.2. This separation prevents routing ambiguities and makes it easier to mirror routes across both ends. If you scale, keep the same non-overlapping rule across every new site and document the pairings in a central vault.
